In the rapidly evolving digital landscape, businesses are in an eternal quest for the elusive competitive edge. The growing appetite...
In the ever-evolving domain of construction, the age-old saying "out with the old, in with the new" has never been...
AS Tallinna SadamAS Tallinna Sadam (hereinafter: Tallinna Sadam) signed an annex to the agreement with the Estonian branch of Akciju...
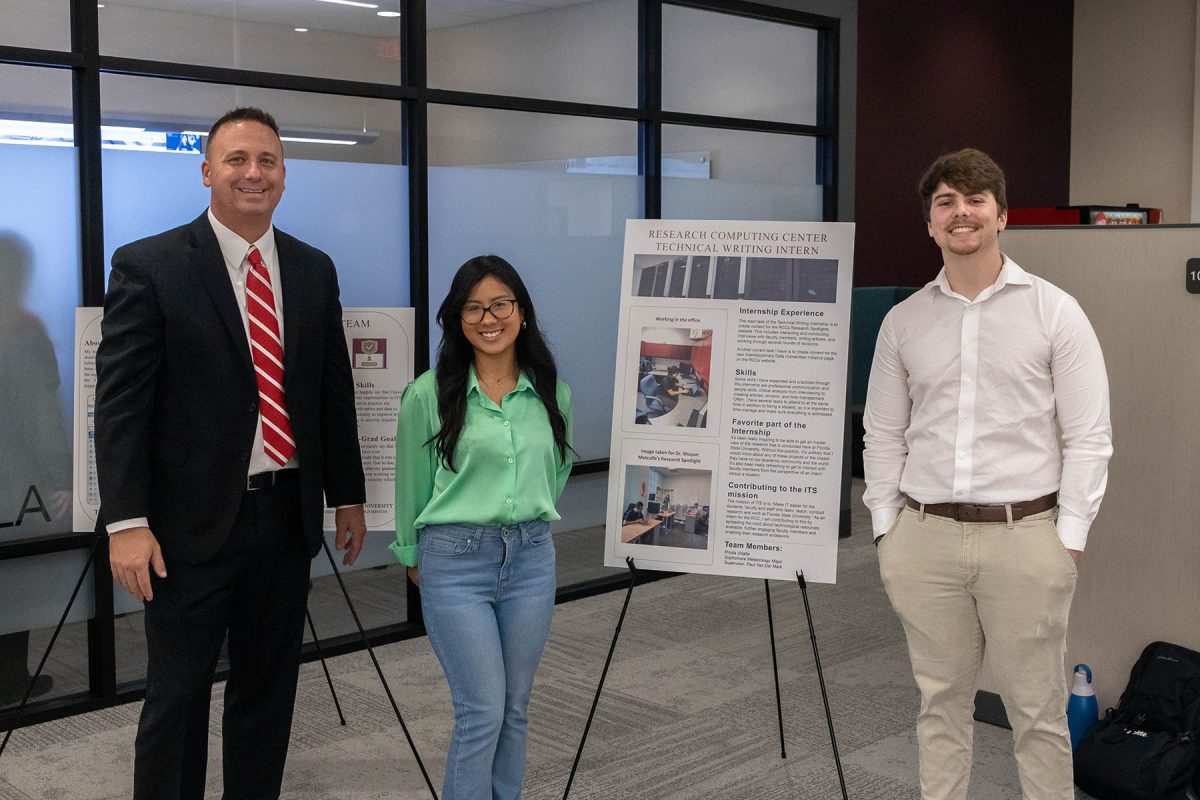
From left, FSU's Chief Information Officer Jonathan Fozard with two interns showcasing their work at the 2022 ITS annual open...
NEWS RELEASE: Presto and T&W Engineering Announce Long-Term Partnership to Advance Wearable Brain Sensing The ASIC on the tester The...
Seattle – Today, the City of Seattle released its Generative Artificial Intelligence (AI) Policy to balance the opportunities created by...
Hema Ramamoorthy, data and AI lead at Digital Catapult discusses how artificial intelligence can help construction tackle some of its...
A ribbon cutting ceremony held Friday marked the grand opening of a new data science and information technology building on...
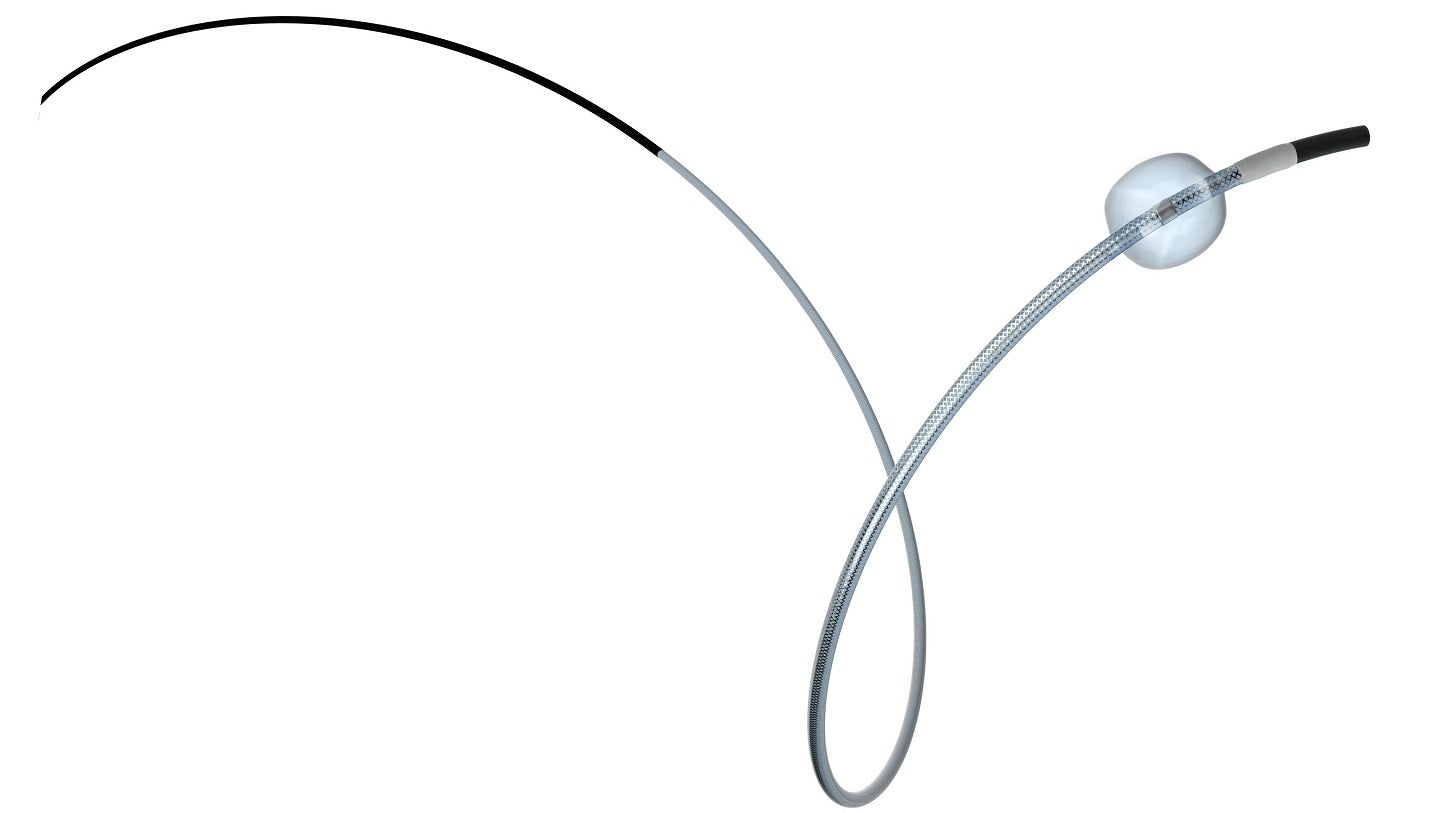
Embolx’s Sniper Balloon Occlusion Microcatheter. Credit: Embolx/PRNewswire. Minimally invasive medical devices maker Embolx has partnered with advanced medical equipment distributor...